Techtalk: „Privilegierte IT-Konten erfordern einen besonderen Umgang“ - IT-techBlog: Cybersecurity & Cloud
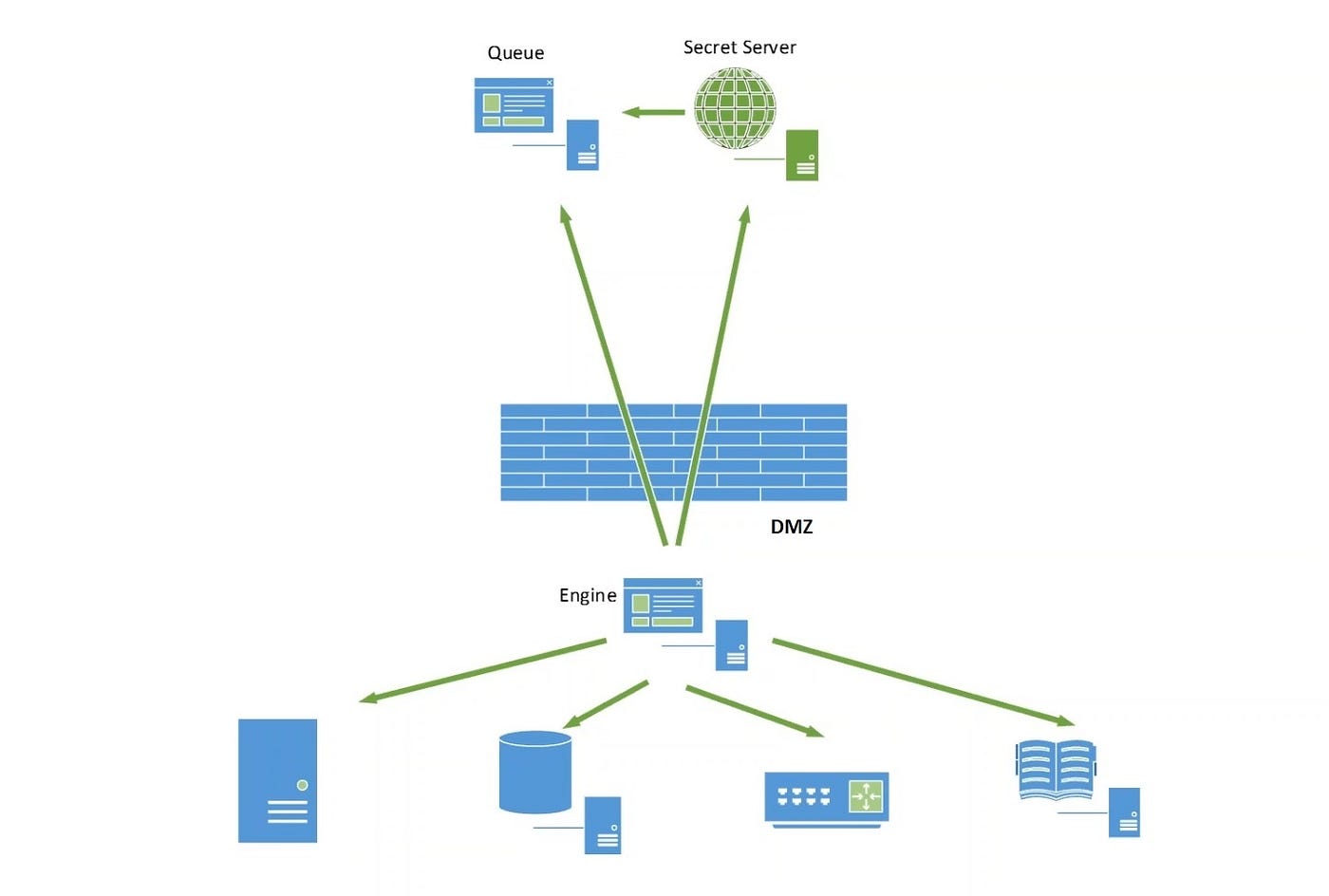
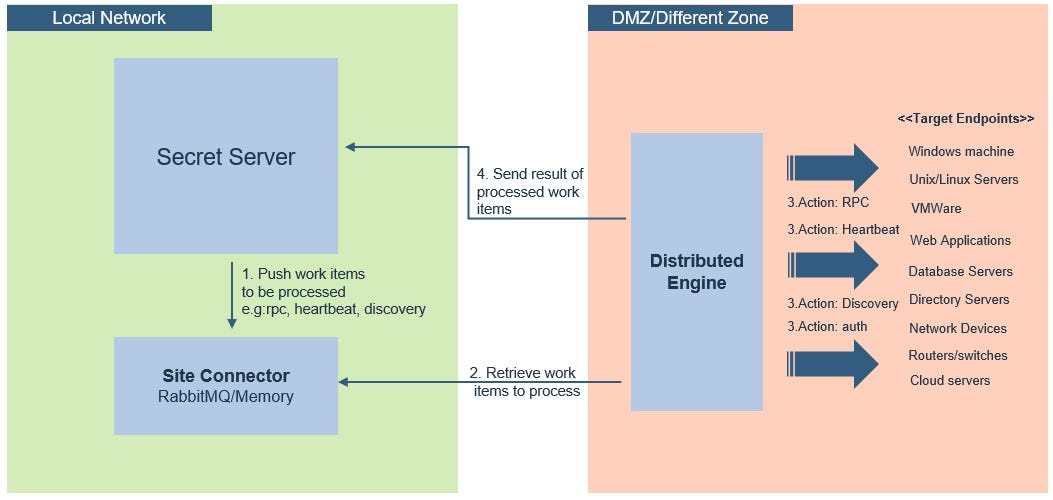
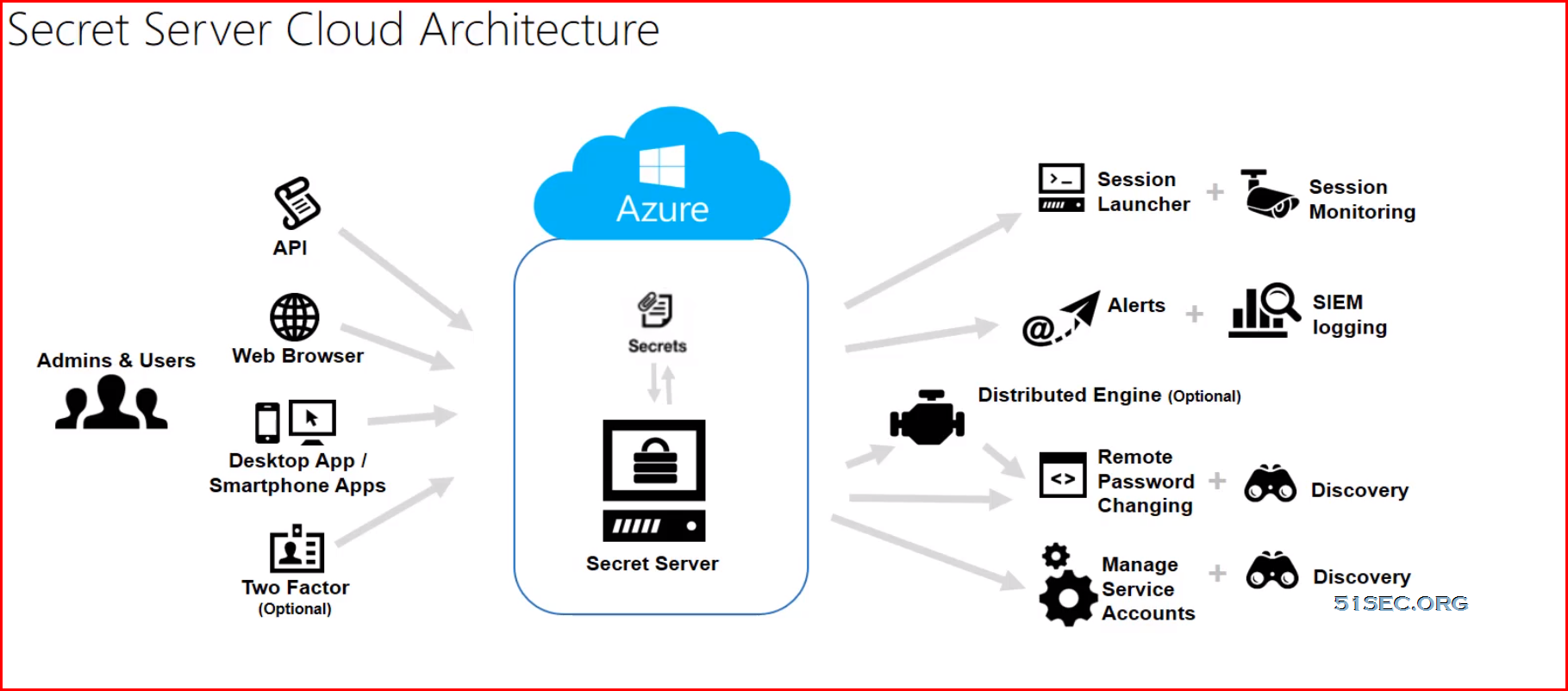
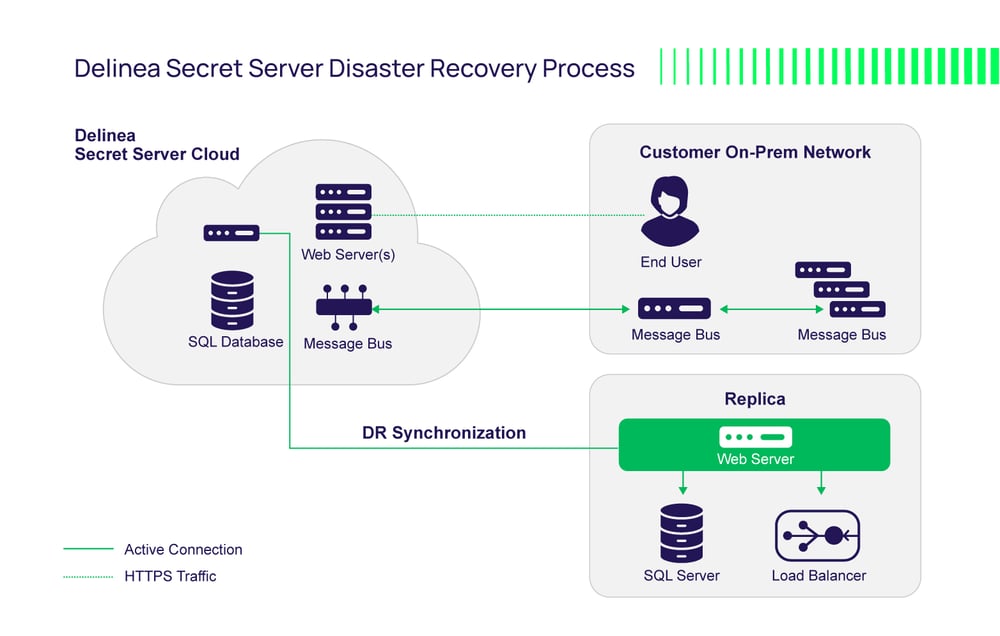
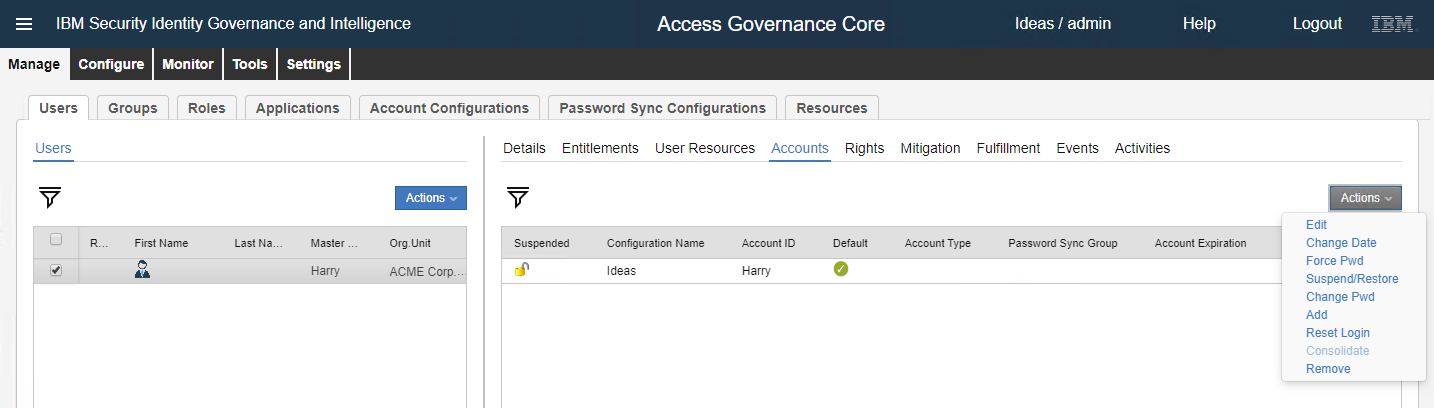
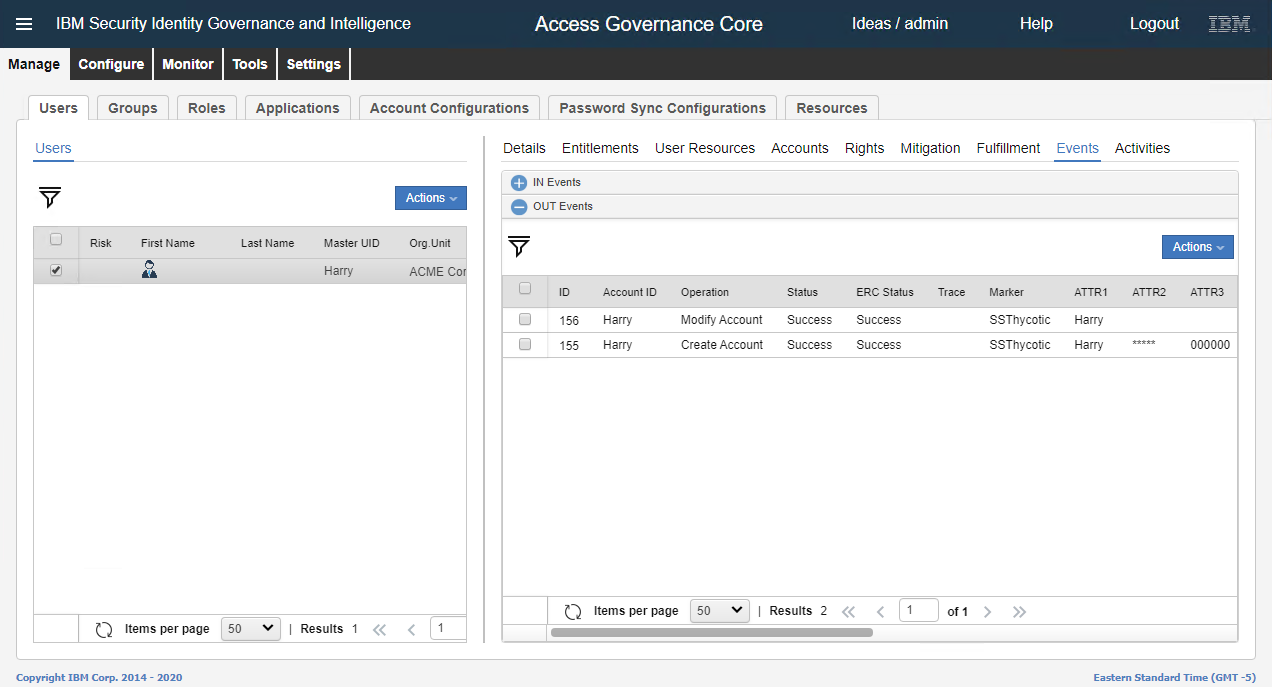
Why Distributed engine is essential to have in IBM Secret Server/Thycotic SS PAM deployment | by Devendra Andhalkar | Medium

Secret Server - Creating a Secret Template for Unix Account key authentication only (wthout password)
IBM y Tech Data te invitan al webinar IBM Security - Secret Server - Advanced Solutions en Hola TD SYNNEX