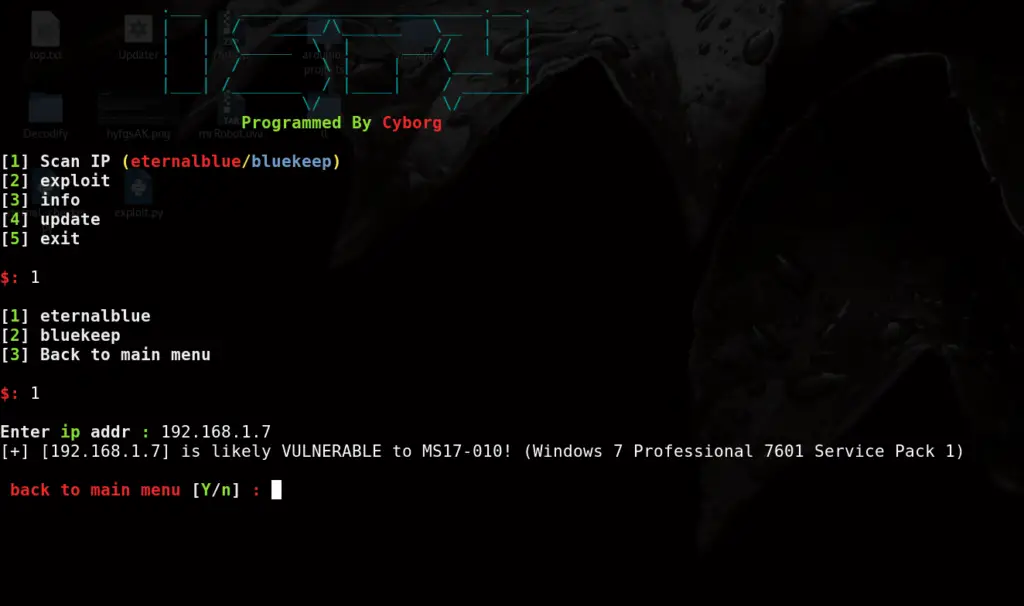
ISPY: Exploiting EternalBlue And BlueKeep Vulnerabilities - Penetration Testing Tools, ML and Linux Tutorials
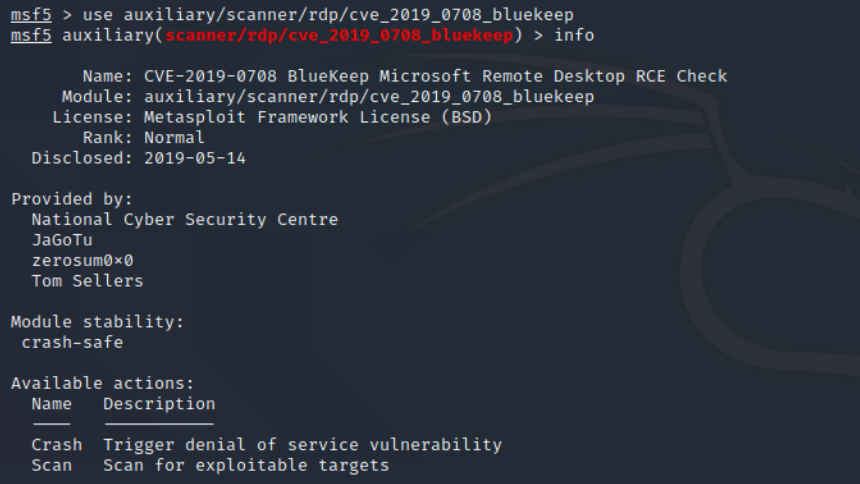
OccupytheWeb on X: "Metasploit Basics for Hackers, Part 1: Getting Started with Metasploit #metasploit #metasploit4hackers #infosec #cybersecurity #cyberwarrior https://t.co/JwRMPNFOER https://t.co/igWTwPsT4c" / X